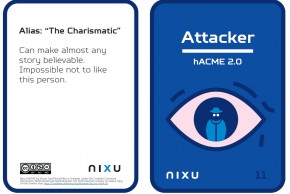
Press release, February 12, 2024, 11:30 EET DNV, the global assurance and risk management provider, has created one of Europe’s fastest-growing cyber security services businesses by merging its existing cyber security business with two recently acquired companies – Nixu and Applied Risk. The merger brings together more than 500 cyber security experts to safeguard demanding IT and industrial control system environments across multiple industries. It follows DNV’s acquisition of Amsterdam-based
Latest News
Blog Post
Publication
NEWS
October 18
Events
May 01
May 07
May 29