How to efficiently plan and prioritize your cybersecurity investments
As CIO and CISO, you continuously need to make decisions. Some decisions force you to go one way or the other – you cannot have both. Management relies on your expertise, and they have empowered you to make the right decisions when it comes to cyber risks, finance, and competences.
But do you have the knowledge and the overview when it comes to the constantly changing cybersecurity landscape? Do you know what are your organization's priority needs in cybersecurity?
Knowledge is power. Or is it?
Knowledge on its own is nothing – but the application of knowledge, that can be highly powerful. If you don't have useful know-how about cybersecurity, you might be doing guesswork and focusing on the wrong actions.
Your business relies on IT running seamlessly 24/7. Today's IT is a myriad of many things, e.g., IoT, infrastructure, applications, business data, end-users, processes, and compliance. You need to handle all of the above to prevent from getting compromised or losing business-critical data.
How to gain knowledge
There are several ways of gaining knowledge to base your decisions on. Based on our experience, you will get the most useful insight for planning and prioritization with the following elements:
- Risk assessment: A risk assessment identifies hazards and risk factors that have the potential to cause harm in your business and evaluates the risk associated with them. It also determines appropriate ways to eliminate the danger or otherwise control the risk.
- Security Information and Event Management (SIEM): SIEM is a software solution that aggregates and analyzes activities from many different sources across your entire IT infrastructure. SIEM collects security data from your network devices, servers, domain controllers, and more. SIEM stores, normalizes, aggregates, and applies analytics to that data to discover trends, detect threats, and enable your organization to investigate any alerts.
- The threat landscape: Make sure that you're up to date on the current threat landscape. Ask for advice from your trusted cybersecurity advisor or sign up for threat landscape reports from, e.g., your local government or cybersecurity organizations. It's essential to be aware of the overall threat landscape but also to keep an eye on threats that primarily target your industry.
- War room: Simply waiting for a security breach is not the right strategy. Create your own war room – not only with IT but also with the management team and exercise and test your incident readiness regularly.
Plan and prioritize
When you know your risks, have enough insight from tools like a SIEM solution and threat reports, we recommend that you plan your yearly activities. It gives you a holistic and outlined approach to cybersecurity.
Based on the activity plan, we recommend that you create an improvement plan covering the next 2-3 years. Here it's important to distinguish between complexity and business value. Start with the tasks that have the most business value and only demands a small effort.
Does cybersecurity create business value? Download the ROI of Cybersecurity Investments whitepaper to learn how to make cybersecurity a competitive advantage »
Cybersecurity roadmap
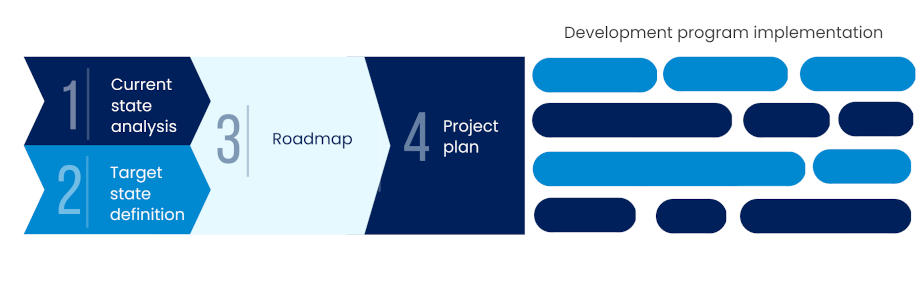
The changes in your business may be rapid. However, you can still ensure that you are doing the right things to develop your cybersecurity optimally. At Nixu, we help you to improve the cybersecurity maturity of your organization by producing a prioritized Cybersecurity Roadmap. This way, you can efficiently plan and prioritize cybersecurity investments. A cybersecurity roadmap gives you a 360-degree view of your cybersecurity maturity level compared to the international framework and industry best practices.
Of course, we understand that organizations can have highly differing resources to manage their threat landscape. Especially startup company management might feel that cybersecurity is impossible to handle with their limited budgets. But even startups can – and really should! – focus on their security.
Rome wasn’t built in a day – and even the best cybersecurity roadmaps grow from small beginnings. The important thing is to take action and start somewhere. Read more here about how to prioritize and begin making cybersecurity investments in your company when every penny counts.
Want to keep track of what's happening in cybersecurity? Sign up for Nixu Newsletter.
