Pressmeddelande, 12 februari, 2024, 11.30 EET DNV, global leverantör av kvalitetssäkring och riskhantering, skapar ett av Europas snabbast växande företag inom cybersäkerhetstjänster när DNV:s befintliga cybersäkerhetsverksamhet går ihop med de nyförvärvade företagen Nixu och Applied Risk. Sammanslagningen samlar över 500 experter inom cybersäkerhet för att skydda krävande IT- och industriella system inom flera branscher. 2021 förvärvade DNV den Amsterdam-baserade industriella
Nyheter
Blogg
Ladda ner
Ladda ner
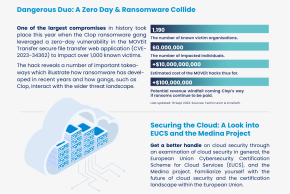
October 18