CISO Says…’How to secure your ICS environment?’
Do the names Industroyer/CrashOverride, Stuxnet, Blackenergy 2, Havex and Triton ring a bell? These are the names of malware targeted at Industrial Control Systems (ICS). Targets were electric grid operators, Iran’s nuclear facilities and Saudi Arabian petrochemical plants [1]. But even non-ICS targeted malware, like Petya [2], may have an impact on industrial control systems. NotPetya ransomware wreaked havoc at Maersk’s APM Terminal in Rotterdam. IT related crime has already infiltrated ICS. What can we do to protect existing systems without causing downtime?
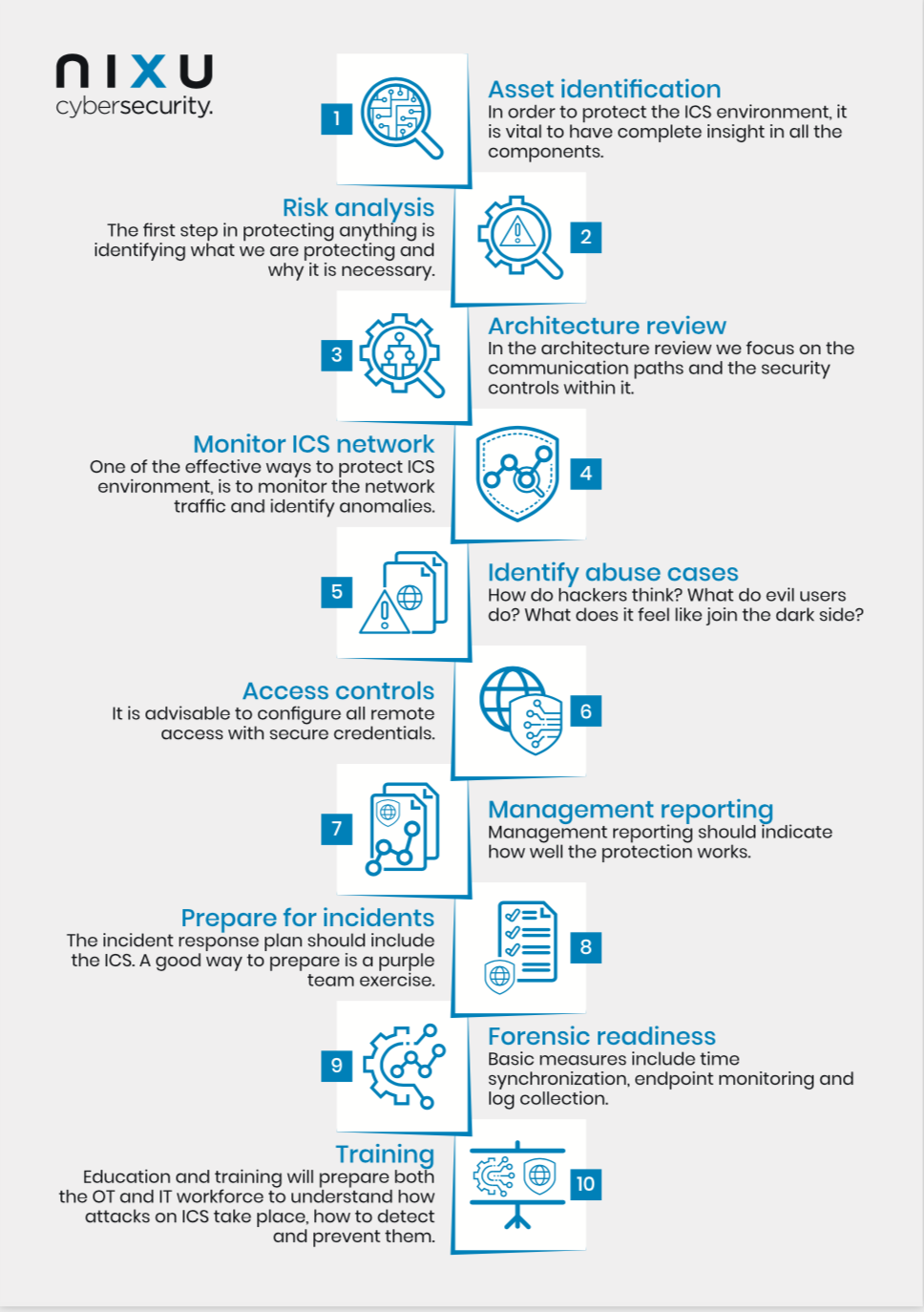
Industrial control systems (ICS) are designed with safety in mind, and cyber security issues were not taken into consideration. Contemporary ICS designs incorporate cyber security, but older installations may be unnecessarily vulnerable, and, in many cases, there is little documentation available. The adage of isolation no longer holds, while this was the one and only protection against cyber-attacks. While it may be true that many components cannot be updated with more secure firmware, and documentation remains an issue, there is still a number of measures that can be taken. Based on Nixu’s decades of experience we compiled an actionable top 10.
1. Perform an asset identification
To in order to protect the ICS environment, it is vital to have complete insight in all its components. Often, the documentation is incomplete, and an inventory is the best way to identify all assets. One way to do this, is to monitor the network and identify the ‘talking’ devices. Some devices will only ‘talk’ when asked and may be undetected. To detect them we ask operators to perform certain tasks, like reading the set points. We do not recommend to actively scan ICS networks with possibly unknown devices, because the scan might interfere with the correct working of the ICS. Another manner of identifying all assets, is to perform a manual or semi-automated assessment, either by yourself or by a trusted partner
2. Perform a risk analysis
The first step in protecting something is to identify what we need to protect and why protection is necessary. This is followed by multiple other considerations: What production processes are delicate? Could manipulation cause physical damage? What happens when there is an uncontrolled shutdown? What is the cost of downtime? And what are the current capabilities to prevent, detect or respond to this?
3. Perform an architecture review
The next step is carrying out an architecture review, where we focus on the communication paths and the security controls within an architecture. Questions are raised such as: how is the Purdue model applied? How are the networks separated? Are there remote connections? What network protocols are used and where?
The architecture provides a blueprint of the network, and what protocols to expect in various network segments. It is important to choose a suitable point in the network to monitor. For example, when redundant networks exist, it might very well be possible we lose sight completely when the incident forces network traffic on another route we do not monitor.
4. Apply access controls
If you can touch it, you can break it
Standard usernames and passwords are commonly found in older systems. Support contracts often demand specific settings and do not allow passwords to be changed. However, it is advisable to at least configure all remote access with secure credentials. This includes dial in modems, GPRS modems, radio modems, VPN’s, RDP, VNC, TeamViewer, etc.
One of the best-known cases of a disgruntled employee antagonist, is the hacking of the Maroochy Shire sewage control system [3]. A former employee made use of the fact there was no access control at all in the radio connection between the central computer and the pumping stations. He triggered the system, causing millions of liters of raw sewage to spill into local parks and rivers.
5. Monitor your ICS network
One of the effective ways to protect an ICS environment, is to monitor the network traffic and identify anomalies. It allows you to detect rogue devices and misconfigured networks and detects successful or failed login attempts into ICS systems. The Network Intrusion Detection System (NIDS) must be capable of understanding the protocols used. Only then it is able to detect anomalies like devices using new protocols, devices connecting to unusual devices and communication of out-of-range process values (like illegal values for set points).
An important step is the identification of alert triggers. What events should generate an alarm? Indicators of compromise might be: login attempts outside working hours, DNS traffic, change in top-10 talkers, decreased stability of ICS connections, high number of TCP retransmissions and out-of-range process values.
At the same time, it should be decided how and when alerts should be handled. In an ICS environment it is usually not advisable to take automated action on an alert. Usually an operator should be notified as quickly as possible, so that immediate action can be taken. Depending on the situation you may want to develop 24x7 monitoring capabilities or only capabilities during business hours. Monitoring a network is only effective if alerts are quickly, and properly responded to.
6. Identify abuse cases
Many of us would like greater insight into how hackers think. In IT we use ‘evil user stories’ [4] when developing secure software. In the ICS environment however, this concept is very useful too. When taking steps to protect infrastructure, it helps to have an idea of who the attackers might be and what actions they are likely to pursue.
It’s good practice to ask specialized ICS penetration testers, within your organization or with the help of a partner, to develop some scenarios. They have experience with many different systems and attack vectors and will provide you with a hacker’s view of your networks. It also supports you in developing security capabilities: what is relevant for your organization and what not? Take the business context of your organization into account to define the cases.
7. Generate management reporting
Management reporting should indicate how well the protection works. It should ensure management the protection is effective. Typical metrics are: mean time to respond (MTTR), visibility or coverage (percentage of devices monitored) and the security maturity level. Also, management reporting based on security controls, can support compliance efforts towards specific frameworks, such as IEC 62443 or NIST.
8. Prepare for incidents
The incident response plan should include the ICS. How should staff respond to an attack on the ICS? A good way to prepare is a purple team exercise. In this exercise the attacker (the red team) is an experienced ICS penetration tester who is working together with the ICS management team, who are defending the ICS (the blue team). The main goal is to train the blue team to detect and stop the attacker. A test environment reflecting the production as precise as possible is a prerequisite for this type of training.
9. Setup forensic readiness
In case of an incident we need information to find out what happened. ‘Forensic Readiness is the achievement of an appropriate level of capability by an organization in order for it to be able to collect, preserve, protect and analyze Digital Evidence so that this evidence can be effectively used in any legal matters, in disciplinary matters, in an employment tribunal or in a court of law’ CESG, Good Practice Guide No. 18, Forensic Readiness [5]. Basic measures include time synchronization, endpoint monitoring and log collection and can be very helpful in reducing the impact of an incident.
10. Train your people
People (62%) present the greatest risk for compromise to an organization’s OT/control systems—not surprising, because the human element lies at the heart of cybersecurity incidents and breaches [6]. Awareness, education and training will prepare both the OT and IT workforce to understand how attacks on ICS take place, how to detect an attack and how to prevent an attack being successful.
Our top 10 list is not exhaustive. It lacks good practices like applying a solid security policy, software security updates, Anti-Virus, hardening, proper network segmentation, physical security and backup and restore. Of course, you should have a proper change management process and handle portable media carefully.
You should also expect the risk to increase as attackers get more sophisticated. We probably can expect ransomware to evolve into ICS systems where attackers take over the ICS and threaten to destroy productions facilities for a ransom.
It will also become of utmost importance to acquire actionable threat intelligence. Assume there is no air gap between your ICS, the IT network and even the internet. Assume the attacker knows every detail about your ICS, obscurity is not security. Keep it cool and don’t be afraid to ask questions. If you are reading this blog post, that means that you already taking the first steps in improving your ICS Security.
Sources:
[1] https://dragos.com/wp-content/uploads/CrashOverride-01.pdf
[2] https://blog.indegy.com/petya-ransomeware-wiper-ics
[3] https://www.risidata.com/Database/Detail/maroochy-shire-sewage-spill
[4] https://www.nixu.com/blog/cyber-attack-motives-part-2-evil-user-stories
[5] https://www.nationalarchives.gov.uk/documents/information-management/forensic-readiness.pdf
[6] SANS 2019 State of OT/ICS Cybersecurity Report, p3
Want to keep track of what's happening in cybersecurity? Sign up for Nixu Newsletter.
