What happened in Cyberlympics? Nixu’s travel blog from the international hacker competition
Cyberlympics is an international cybersecurity challenge, where teams all over the world take part in a two-phase contest. The qualification round is a 12-hour Capture-the-Flag (CTF) style competition, from which top-2 from each region advances to finals. The final round is held on-site, this year in Canada. Here’s our travel report from the international hacker competition.
The qualifiers that almost left us out
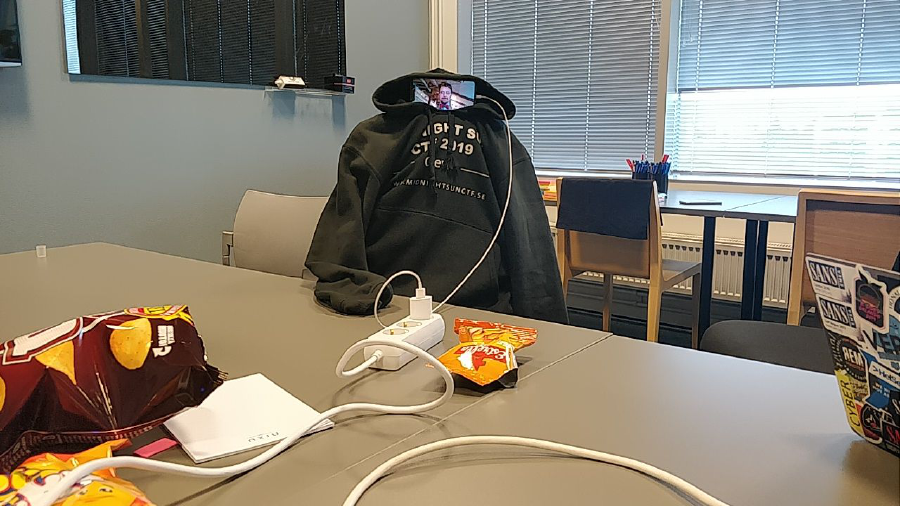
The qualifiers took place on Saturday, September 7th. The 12-hour playing time is from 00.00 to 12.00 in UTC, so in Finland, the game starts exotically at 03.00 AM. Usually, it is more fun to play CTFs together, so we had reserved a meeting room at the Nixu Espoo office. Oh boy, how crispy it felt to wake up on Saturday at 02.00 AM and travel voluntarily to work!
This year the CTF platform worked well, and the competition started when it was supposed to. The challenges varied from stegoburgers to hacking. Unlike last year, reverse and web pen-testing did not play a big role in the elimination round.
During the game, we kept our position in the global top-3, most of the time top-2. Team called MapleL33ts were overpowered, but we had a great race for the second place with Jobless Hackers. We finally were defeated by them, and we finished 3rd with a 200-point margin to the 4th team.
As the 3rd place was among the best performances of TeamNX history in the Cyberlympics elimination round, we were pretty confident to have a spot in the finals. It turned out, we were wrong: both teams above us, MapleL33ts and Jobless Hackers, were from Europe. Since only two teams from each continent are qualified to the finals, we were out.
However, Cyberlympics contacted us, telling that MapleL33ts were not able to participate in the final round. That meant that we were going to Canada! Whoop whoop!
Off to the competition site
This year the finals were held in Oshawa, Canada, on October 26th. We traveled to Toronto a few days early to catch the time difference and to build team spirit. This year's TeamNX was a mix of specialists from Security Engineering and Managed Security Services. The competition started quite early, which gave a small advantage for teams traveling from the east due to the time difference.
The finalists were transported from a hotel to the competition venue together. At the venue in Durham College, competition rules were reviewed, and teams guided to their seats. TeamNX's spot was different than others’ as it was in the lobby of the competition hall. At first, we didn’t like being separated from others in a hallway where people were coming and going. The competition organizers talked us around, and we decided to stay in the given spot.

It turned out that the hall spot was quieter than the actual competition room, and we were able to focus on challenges without distraction from other teams. The downside was that a lot of people interested in the competition stayed on our spot and wanted to see us doing live stuff. It's not always nice to hack when someone is behind your shoulder surfing you. :-)
Mysterious USB stick
Every team was given a USB stick and no instructions on what to do. To get access to the game network, every team had to solve the first challenge or buy access with 150 points. We were able to image the USB stick quite fast and start forensicating it. We saw it was TAILS (a Linux distro for tinfoil hats) with LUKS encrypted partition. We first though the task was to brute force the password of the LUKS partition. The rules denied using cloud computing or external systems, and we did not have computing power with us, so we decided to try it with our normal office-tier laptops without GPUs.
After running a few rounds of hashcat against the LUKS password around 7 hashes per second, we thought there must be a hint of the password somewhere on the USB stick. We compared the boot partition with a TAILS downloaded from the Internet and found out it was the same. After that, we managed to carve some data from the USB stick, but there was nothing relevant.

We did not feel we proceeded with the challenge, so we decided to buy the access with 150 points. After the competition, we found out the task was to brute force the password, and we were doing the right thing. Few of the teams had gaming laptops with them and were able to crack the password around 7 seconds. Most of the teams did not solve the first challenge, most likely due to the same reasons as we.
Enter the real challenges
After paying the 150 points, we got access to the game network. Few challenges were already open in the web portal and we started working on them. We had a local CTF pad running where we were easily able to share answers among us without saying them out loud. We managed to solve many challenges quickly and ground up the scoreboard. Most of the challenges were some kind of services running on the local network where we had to send some kind of payload to get the flag out. Few webservices crashed after we disrupted them and the rules said organizers are not willing to get them back up. Because of this, we lost a ton of points and did not get a chance to try solving them.
In the last few hours, we did not have that much to do as we had solved almost every running challenge. However, there were three extra challenges where we did well. These challenges had limited time and only two members of the team were allowed to do them. The first of them was lockpicking, where we managed to get some points. The second one was a CCTV camera, which we had to hack in 15 minutes and turn it off. We found public DoS exploit to camera management web interface and executed it with success to gain full points from the task.
The third challenge was more playful competition against a randomly chosen team and had three parts: a puzzle, assembly of Legos, and a sort of 3D puzzle. We were faster and got some points. The scoreboard got hidden sometime before the time ran out and if I recall correctly, we were standing fourth place but did not have submitted all the flags yet. We calculated the points we got after blacking out the scoreboard and thought we were either 4th or 3rd in the competition.
The prize ceremony
The time run out and we were transferred to our hotel from the venue. We had a moment to get our shit back together before transportation to the prize ceremony. The prize ceremony was also held in Durham college, and the venue was really nice. Board of the directors of Durham college and Oshawa county had all gathered suited up to the place and we had some good food and drinks there.

After speeches, top-3 of the competition was revealed and awarded with cool prizes.
Unfortunately for us, our sprint failed, and we finished 4th. The winners were Jobless Hackers from the Netherlands, whom we raced on the elimination round for the 2nd place. We would like to congratulate them on winning the competition and promise we will race them next year again!
Want to keep track of what's happening in cybersecurity? Sign up for Nixu Newsletter.

