PCI DSS 4.0 is here. What should I know about it?
Someone wise once said that change is the only constant. That is also true in the payment card industry as PCI Security Standards Council (PCI SSC) recently released the next version of the PCI DSS standard. This new revision, version 4.0, is the most significant update to the standard since 2013 (when PCI DSS 3.0 was released) and it will have an impact on all stakeholders in the PCI DSS industry.
As you already may imagine, in digitalized society, technologies and the threat landscape have evolved quite a bit since 2013, so this new revision of the PCI DSS is a very welcome update.
In this blog post, I will provide some highlights of the new PCI DSS 4.0: what has changed, what is new, what will be the next steps and when the transition to 4.0 should be completed.

But before going to the details of PCI DSS 4.0, what is PCI DSS?
PCI DSS (Payment Card Industry Data Security Standard) is the de facto security standard for protecting payment card-related information (cardholder data). It applies to all entities that in their operations store, process, or transmit payment card information or can otherwise impact the security of such information. These kinds of entities are, for example, payment service providers, data centers hosting payment card-related environments, or merchants accepting credit card payments in their stores or e-commerce. PCI DSS is maintained by the PCI Security Standards Council (PCI SSC), founded by payment card brands.
The standard sets the minimum requirements of the payment industry. I encourage all to conduct a risk assessment of their environment and implement additional controls to address their own organization’s threat landscape.
Timeline and impact for organizations
The transition from PCI DSS 3.2.1 to new PCI DSS 4.0 requires time and resources to prepare and implement solutions to meet new and changed requirements. Once implemented, it is also important to ensure that there are sufficient resources available to operate new controls and compliance with PCI DSS 4.0. For organizations that store, process, or transmit cardholder data in their operations, the change is more significant than for others.
For merchants who themselves do not store, process, or transmit cardholder data but utilize payment service providers’ payment terminals or e-commerce solutions (redirect or iFrame), the impact may be smaller. However, the change still requires sufficient resources, careful planning, and implementation.
One of the most interesting changes in PCI DSS 4.0 is that it introduces more flexibility for organizations to meet the standard requirements. Instead of directly implementing controls defined in the standard, the organizations can choose a customized approach to meet the standard requirements and their intent. This will allow organizations to implement the PCI DSS requirements in a tailored manner befitting the organization and their environment. This approach is intended for more mature entities that already have well-established practices and risk management routines. A customized approach also requires customized PCI DSS assessments, necessitating the assessor to derive appropriate testing procedures for each approach.
Organizations do not have to select between the “traditional approach” and a customized approach and stick with that selection. You can implement some of the controls in the “traditional” way and some of the controls in a customized manner. This will help you avoid, for example, scenarios where you need to implement something only because it is required. Instead, organizations can choose to implement truly meaningful controls that not only meet the industry requirements but also fit the organizations’ technical infrastructure and threat landscape.
PCI SSC has also recently published supporting documents for PCI DSS 4.0, which further clarify the changes and their impact on organizations. Additionally, PCI SSC will start providing training to the assessors in Q2/2022, after which assessors will become eligible to conduct PCI DSS 4.0 assessments.
There are 64 new requirements, of which 11 are only applicable for service providers. Majority of the new requirements are best practices until the 31st of March 2025, after which they will become mandatory automatically. The remaining 13 requirements are effective immediately after the organization starts using PCI DSS 4.0. In addition to the new requirements, many of the old requirements have evolved.
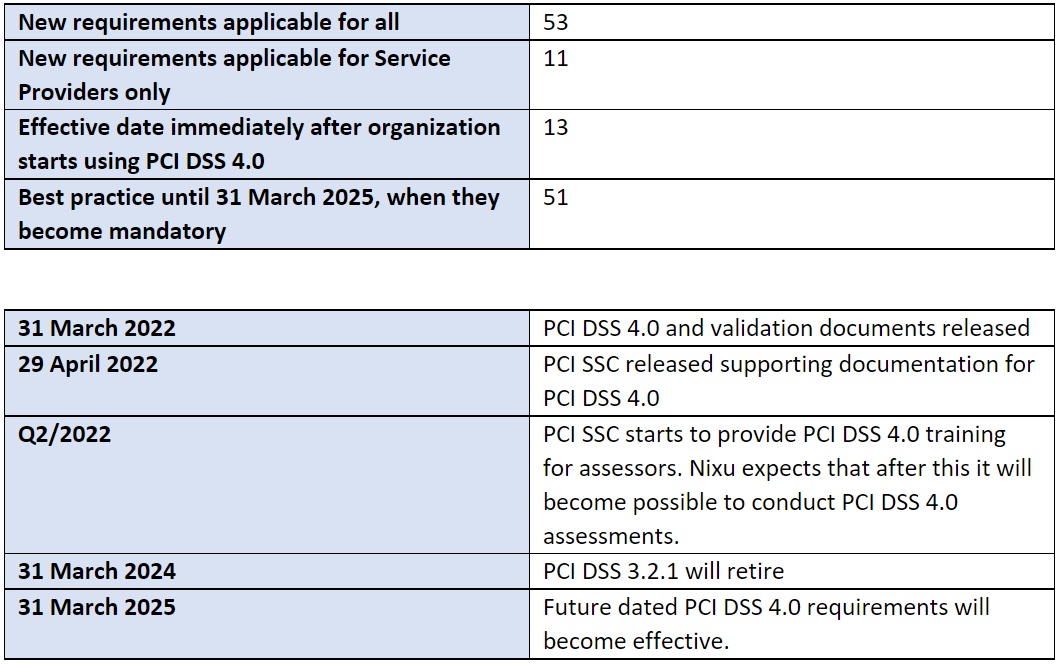
The transition period to the new standard version is already ongoing. During the transition period, it is still possible to use PCI DSS 3.2.1. So, there is no need to switch to the new version in a hurry. That said, there is no time to waste either, as PCI DSS 3.2.1 will inevitably retire in two years. Organizations should start analyzing this change and its impact on their environment. After that, one should begin planning how to implement these new or changed requirements on time.
Nixu and PCI DSS
The first version of the PCI DSS was published already in 2004, and Nixu was one of the early adopters of the standard, conducting PCI DSS assessments and supporting companies to incorporate PCI DSS into their environments. Nixu has been pioneering PCI DSS implementations and assessments in Finland and has extensive experience in various PCI DSS environments and implementations.
Nixu can help your organization recognize, define, and implement the changes needed to transition from PCI DSS 3.2.1 to PCI DSS 4.0. With our Advisory team, we can create, provide, and facilitate training and exercises, and our Advisory PCI as a Service can help you operate and maintain your PCI DSS compliance.
Nixu Certification is an independent team solely focused on auditing and assessments. Nixu Certification provides PCI DSS assessments across Europe. Immediately when it becomes possible, we will start providing PCI DSS 4.0 onsite assessments.
In addition to PCI DSS assessments, Nixu Certification provides the widest choice of information security audits in Finland.
Nixu provides technical testing that meets PCI DSS requirements. Examples of such technical testing include penetration testing, segmentation testing, or vulnerability scanning.
Would you like to know more about PCI DSS 4.0 or PCI DSS in general and how we could help you with it? Do not hesitate to contact us, we are here to help you!
Ville Koskinen is Nixu Certification’s experienced Senior Security Auditor and PCI Qualified Security Assessor, who has led and participated in numerous PCI DSS assessments. Ville is also the Product Manager for Nixu Certification’s PCI DSS services.

