Preparing for the unknown – The five biggest cybersecurity trends to keep an eye on
While digitalization took major leaps during the past year, it should be noted that most cybersecurity trends have been around for a while. Thus, many changes that are likely to happen in 2021 should come as no surprise. However, being aware of something doesn’t mean you’re prepared for it. In 2021, the rate of change will continue to accelerate, and organizations must rise to the occasion.
We at Nixu believe that during the next five years, the most markable effects to the cybersecurity market will come from Industry 4.0, rising role of small and medium businesses (SMB), distribution of defense in the cloud era and the change of perimeter due to zero trust and beyond corporation ideologies.

Based on this long-term vision, we have listed five cybersecurity trends every organization should pay close attention to:
1. REMOTE WORK CONTINUES
The pandemic forced organizations to rush in updating their digital capabilities as well as securing their processes and devices. Remote working has become the new normal in many industries, due to which there is an urgent need to ensure the defenses we built last year are still up and valid.
Nixu’s tips
Keep up the good work – the cybersecurity culture you’ve built needs to be fostered. To make the good habits stay, we must reinforce user awareness and continue improving threat detection capabilities. While the pandemic may affect budgets and resources, remember that sparing the buck in cybersecurity may begin to degrade operations. Security is not the place to save.
2. WATCH OUT FOR RANSOMWARE
Ransomware will continue to be a large threat to organizations of all sizes. While large companies make the most interesting targets, SMBs will continue to get hit. Blackmailers have switched tactics to force their victims to pay and they are often performing a combination of environment lockdowns, public shaming via data leaks and selling data to the highest bidder. The change in attacker tactics complicates business recovery and forces organizations to focus more on preventive actions.
Nixu’s tips
Attackers don’t care whether they get their money from small, medium or large businesses – ransomware affects everyone. Thus, every organization must be able to detect threats and understand their surroundings. Patched systems, minimal attack surface, well-educated users and proper threat detection reduces the risk of getting breached – it’s all about the basics.
3. ADOPT ZERO TRUST THINKING AND CLOUD NATIVE SERVICES
Zero trust thinking and cloud native services require a change in mindset. The ability to map out what we have, what we know and what we need to learn is crucial. Identity and access management’s role will increase since organizations cannot rely on traditional perimeter thinking when it comes to their employees, at least not as much as they have in the past.
Nixu’s tips
It is a great misconception that once everything is in the cloud, someone else will defend the business assets. Even though “someone else provides” the service, organizations must understand how their information is utilized, who has access to it and what to do if it ends up in the wrong hands. Therefore, organizations must be able to monitor their user accounts’ behavior, use of their data and have reliable means to identify users.
4. INDUSTRY 4.0 CHANGES THE GAME
Industrial organizations are beginning to understand how connected their critical assets, Operational Technology (OT) environments, truly are and thus put more effort into securing them. Connecting OT systems to internet offers clear business benefits, but the truth is not all machines were made to work online.
Nixu’s tips
Network segmentation, secure remote access, asset discovery and threat detection are the first things to solve.The key is yet again to understand what our current state is, what really needs to be secured and how.
5. THE POSSIBILITIES OF ARTIFICIAL INTELLIGENCE AND SMART AUTOMATION
Artificial intelligence and smart automation are developing at a tremendous rate, which is why they are becoming a normal part of large-scale cyber operations. In Defensive Cyber Operations (DCO), most common use cases are spam email filtering, anomaly detection in sensors and smart orchestration tools like SOAR (Security Orchestration, Automation and Response). In Offensive Cyber Operations (OCO), attackers can for example use AI to produce counterfeit messages to trick people or even profile network traffic to hide their actions in the environments.
Nixu’s tips
Organizations must be ready to experiment with smarter ways to perform cyber operations. Even though AI still has a long way to go in revolutionizing the industry, it can benefit organizations in multiple ways. The most crucial thing is to understand how it affects business, in both good and bad. As organizations can utilize AI, so can attackers. Thus, the efforts put into defense should be equal if not superior.
Our role in cybersecurity is to defend the mission-critical environment and enable businesses to make enlightened decisions matching their needs. Usually this means that organizations must be ready to adapt to new challenges.
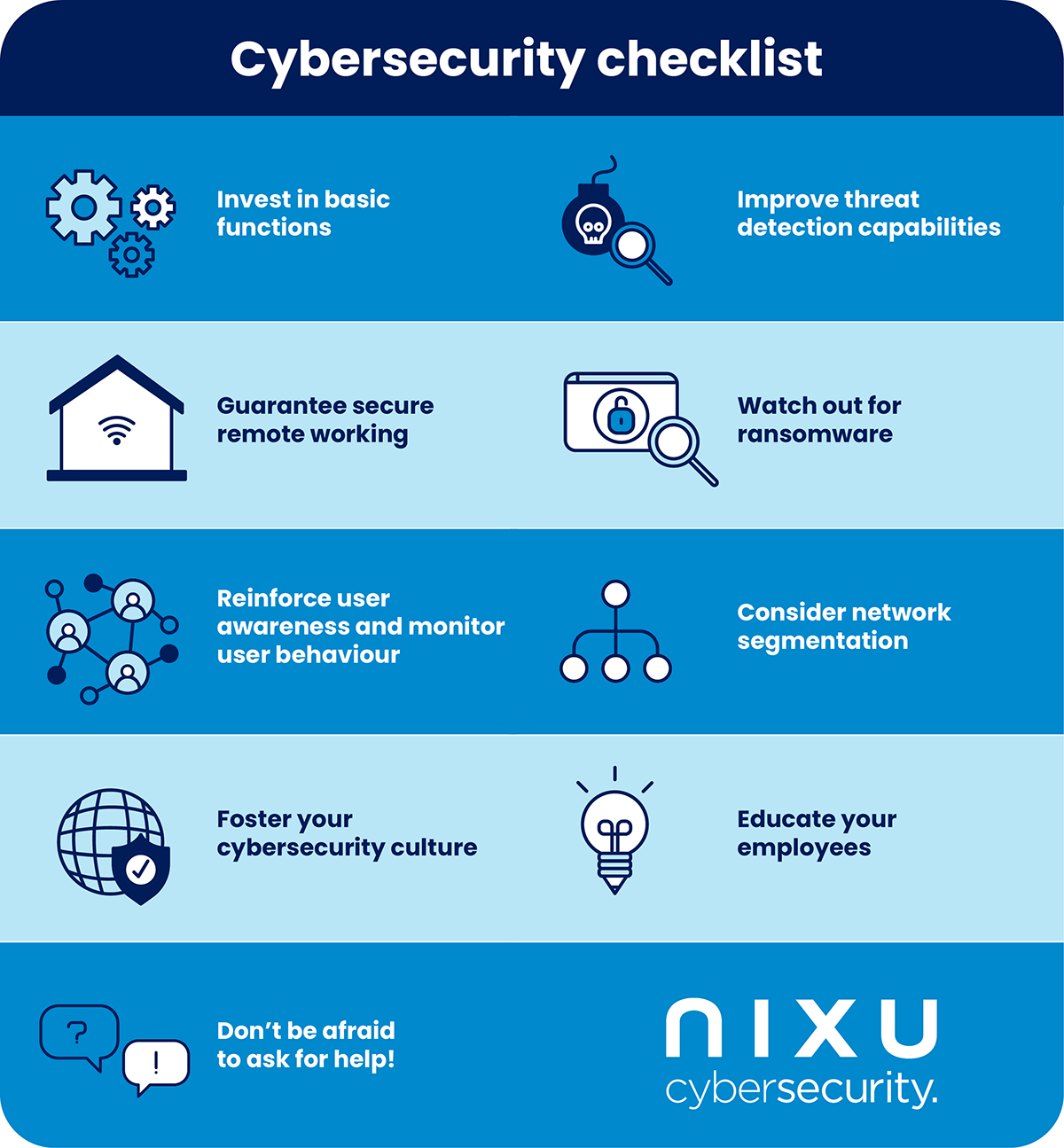
To thrive in the unknow future, the platform must be stable and the basics must be done right. In practice, this means focusing on attack surface mapping, vulnerability and identity management, user awareness, network segmentation, threat detection and incident response. Thus, investing in cybersecurity isn’t always about getting the latest tools, but rather finding ways to manage and monitor new environments with their native tools.
While the industry roots for organizations’ growth in cybersecurity efforts, the field strives for improvement as well. Whether focusing on increasing the diversity of workforce or collaborating more with information security community – the cybersecurity field has some homework too. When organizations and the industry step up their game, only the sky is limit.
That being said, all the basic functions must be done in a modern way, taking into account the trends mentioned above. And with that we are more than happy to help you.
Want to keep track of what's happening in cybersecurity? Sign up for Nixu Newsletter.
