CISO Says... Carry on?!
Are you expecting your IT department to work on a budget and keep things secure? Think again! Because you could probably lift some weight of their shoulders, so they can do more with less.
A few weeks ago, I saw parallels with Expedition Robinson - a reality television program in which contestants are put into survival situations – and the cybersecurity industry. There was a challenge where contestants had to carry sand filled bags around their neck and run a course. The last one to finish had to leave the game and had to choose another contestant to hand over his sandbags. In the last race an unfortunate guy had to carry almost all of the bags and he lost from a girl who had to carry only a few. The weight was so heavy he could barely walk, let alone run.
In IT it’s often the CIO who has to carry all the bags. Departments demand more and more new services, but won’t allow old ones to be removed. The IT department is expected to keep up with the latest technology AND to keep the old systems (often called ‘legacy’) running. The weight becomes heavier and heavier.
This is due to the fact that legacy is harder to maintain. Older applications may need older Operating Systems, older Databases and sometimes even older hardware to run on. Some of these components may run out of supplier support. At that point security patches are no longer available and extra mitigating measures must be put in place. For all the components you need to have expertise but since people want to move on with modern technology (they have a career too), it will become harder to find.
To exploit a vulnerability, an attacker must have at least one applicable tool or technique that can connect to a system weakness. In this frame, vulnerability is also known as the attack surface or exposure. The more different systems in use, the bigger the exposure, the bigger the risk.
At the same time the departments usually only pay for the initial project implementing new systems, but don’t have to pay the maintenance costs. Maintenance is part of the IT budget. Leaving ‘old stuff’ running comes at no cost for them. It’s free shopping, while replacing the legacy will cost them. It is a kind of prisoner’s dilemma[1] between the supplying IT department and the various consuming other departments. They can have an overall better, more secure, IT system if they cooperate and stop acting on individual interests.
Running Legacy is not only insecure, it’s also expensive. decreasing the cost will improve security, but the opposite is also true: Improving security will decrease the costs. Security can have a positive ROI.
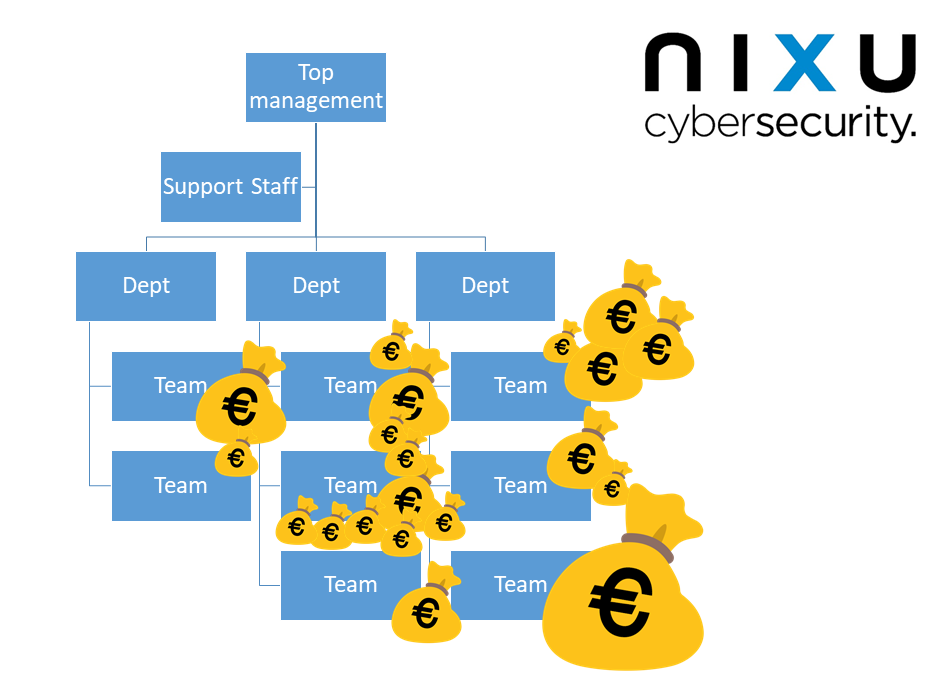
As a CISO you could leverage the cost of IT to improve overall security by making the actual costs of your high- risk legacy applications clear. Analyse the dependencies and take into account that every component needs to be maintained. Then visualize which department is responsible for these hidden costs. In my experience this will trigger an important discussion: Why is the IT budget so unevenly spread? Why does IT carry all the load, while they don’t?
Source:
[1] https://en.wikipedia.org/wiki/Prisoner%27s_dilemma
Want to keep track of what's happening in cybersecurity? Sign up for Nixu Newsletter.
